Layer 1 crypto platform, Solana, offers a faster and cheaper blockchain solution to Ethereum. This is achieved using Proof-of-History combined with Proof-of-Stake consensus. We look at any security implications.Continue readingSolana – does Proof-of-History improve security?
The Ethereum blockchain is about to undergo a major upgrade to version 2.0. In this article we look at what improvements are coming including how Eth2 impacts security.Continue readingEth2 – making Ethereum more secure
In part 2 of this article we continue to examine the risks of holding crypto with a focus on the chances and ways of recovering your cryptocurrency assets if they are lost or stolen.Continue readingRecovering Lost or Stolen Crypto (part 2)
We hear all the time about how secure crypto is and that it is both anonymous & untraceable. In this article we will examine what are the risks of holding crypto and the chances of recovering it if lost or stolen.Continue readingRecovering Lost or Stolen Crypto (part 1)
In this article we examine Stablecoins which are cryptocurrency tokens that are pegged to traditional assets such as the US Dollar. Examples of these are explained together with their uses covered and associated security considerations.Continue readingStablecoins – are these cryptocurrencies risky?
In this article we take a look at the Binance Smart Chain blockchain platform. We understand how it integrates with Binance Chain and supports the development of dApps together with security considerations.Continue readingBinance Smart Chain – is BSC a secure platform?
Ethereum is the second biggest cryptocurrency and forms the basis of many other AltCoins. With smart contract functionality, dapps such as DeFi Protocols, DAOs & NFTs are possible but how secure are they?Continue readingEthereum – a secure Global Computer?
To some Bitcoin is perceived, along with cryptocurrencies in general, to be risky, dangerous and associated with cyber crime. To others it is seen as being extremely secure and provides opportunity as a great investment & hedge against inflation. In this article we examine how Bitcoin works and the security aspects associated with it.Continue readingBitcoin – is Digital Gold secure?
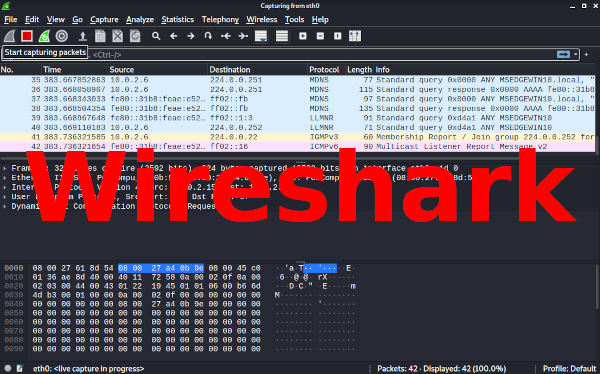
In this article we examine Wireshark which is a graphical network packet analyzer. Wireshark is available on many platforms, supports multiple protocols, and can be used to capture live data that can be analyzed offline.Continue readingWireshark – Network Packet Analyzer
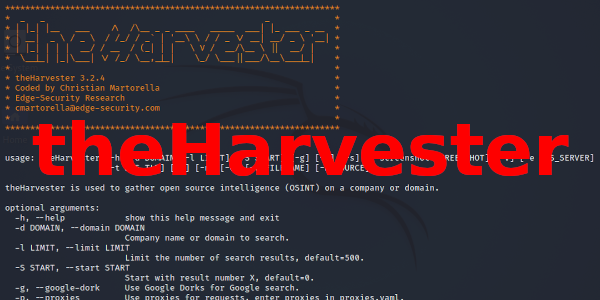
Here we examine how theHarvester can be used to carry out OSINT (Open Source INTelligence) in order to gather emails, names, subdomains, IP addresses and URLs.Continue readingtheHarvester – Open Source Intelligence (OSINT)