Web sites are built using different architectures, based on a variety of platforms, and with a mixture of technologies and purposes. This means that there is no single solution to protect all web sites against every form of online attack. Instead there are different layers of protection and techniques that can be employed to better help defend against potential adversaries.
In the following sections of this article we have grouped together similar areas of protection:
Server security
These forms of defense focus on hardware such as hosting computers and networking devices plus their operating systems.
Anti-Virus
Most of us are accustomed to Anti-Virus software running on our laptop or desktop computers and in some instances also using them on our tablets or smartphones.
Anti-Virus software can also be installed on servers as well as form part of an advanced firewall solution. These can help protect against the following threats on a web site’s server:
- Malware
- Rootkit
Both threats take the form of malicious software being installed on the server and then either infecting code/data or enabling an attacker to extricate information or cause damage to the server or data itself.
For more details on this please check out our article, Selecting the right AntiVirus package.
Deception Technologies
Whilst most defenses employed by web hosting servers or data centers are focused on firewalls to protect against intruders getting in, there are more advanced solutions that concentrate on damage limitation in the event that a firewall is breached.
Deception technologies aim to deceive attackers using decoys and traps. They include a combination of detecting, deceiving, delaying, and identifying intruders.
For more details on these types of solutions please check out our recent article, Cyber Security through Deception (part 1) & (part 2).
Firewalls
In our recent article, Does a Firewall protect against being hacked? (part 1) & (part 2), we identified two main types of firewall:
- Host-based
- Network-based
In a web hosting scenario the host-based firewall would take the form of a program, or suite of programs, installed on a server’s operating system or within a virtual machine (VM). The purpose of this is to protect an individual machine.
The network-based firewall would be installed on dedicated hardware or a router that acts a an Internet gateway and protects multiple machines.
There are many types of firewalls, which are outlined in the aforementioned article, but essentially they all monitor network traffic and try to prevent malicious traffic. This can cover many types of threats including Distributed Denial of Service (DDoS) and brute force attacks plus many others.
Application security
These types of security measures are concerned with the software, databases, and web servers running on the hosting server.
Code
Writing secure code is a major part of developing web-based applications and sites. As part of this one or more of the following should be employed to protect web site users and their data:
- Bugs – proper testing of code should always be carried out because low quality code, poor practices and coding errors can leave flaws that can potentially be exploited by hackers.
- Custom code – many off-the-shelf security packages have known exploits that are shared on hacker forums, exploitation databases and the dark web. Until a fix is implemented then sites using these packages become vulnerable. Developing a custom security solution has both pros and cons:
- Pros – they can be more difficult for hackers to exploit due to being unique or uncommon with the techniques used.
- Cons – limited knowledge and development resources can make custom solutions weak and vulnerable.
- Security API – third party developer solutions are available as API’s or packages that may be open-source (free) or paid for. These are available for many programming languages and can often provide stronger security than the basic ones that ship with a given web server or programming language.
- User verification – there are many hacking utilities that can check high volumes of weaknesses within web-based applications in a short amount of time. To reduce their effectiveness there are a number of techniques that can be employed including ‘captcha’. This involves presenting the user with an additional verification over and above a username/password combination e.g.
- a graphic of a number/text combination with distorted digits/characters and extra lines or dots that act as noise. The number/text then needs inputting for validation.
- a ‘not robot’ tick box that needs completing and is verified by the server.
- a series of pictures whereby all boxes containing a boat, traffic lights or similar need ticking to pass verification.
Databases
There are a couple of security considerations that are important within web-based applications concerning databases:
- Database configurations – any configuration files containing database connection settings, such as username & password, should always be read only, have the correct file ownership, and ideally be located outside of or higher up the HTML directory tree. This protects them from being accessed by potential hackers.
- Password fields – storing passwords in databases is generally discouraged, but if they are to be then they must never be stored as plain text and instead should always be encrypted. This can be achieved by using an encryption function then storing them as text or by using a password field type.
Web Servers
These are web server settings that relate to security:
- .htaccess – these are ‘distributed configuration files’ that are used by some web servers (e.g. Apache) and can be placed in multiple folders. They are usually used on web hosting servers where access to the main configuration files is not available. Any settings within a ‘.htaccess’ file are applied to the current and sub-folders unless overridden further down the hierarchy. Within this file it is possible to specify web server authentication settings e.g.
AuthType Basic
AuthName "Password Required"
AuthUserFile "/www/passwords/password.file"
AuthGroupFile "/www/passwords/group.file"
Require group admins- Configuration files – any files containing settings (e.g. .htaccess, PHP, WordPress etc) should always have the correct ownership, permissions and be located in the most secure location.
- Secure Sockets Layer (SSL) – this is the standard for transmitting information over a secure Internet connection. The data is encrypted and secured using a SSL Certificate. These certificates are installed within the web server and help protect data that is transmitted to/from the web site user from being intercepted.
- Web Server settings – there are a number of web server settings that are related to security of the web sites that are hosted. An example for Apache is ‘indexes’ whereby the “Options -Indexes” setting should be specified for a virtual host so that the contents of a directory within a web folder cannot be listed. The reason for this is so that hackers cannot see the individual files and hence potentially leverage this information. There are other security related settings mentioned within the Apache documentation.
Client security
This area looks at protections relating to web browsers, Internet-enabled devices, and apps being used by online users.
- Password Manager – it is good practice to use strong passwords and different ones for each web site. The problem is that this can make them almost impossible to remember and passwords should never be written down. A solution that can help with this is to use a Password Manager and ideally one that will generate complex passwords and remember them across multiple Internet-enabled devices. See here for more details.
- Strong passwords – using complex passwords for web sites makes them harder for hackers to guess or ‘brute force’ with automated attacks. Using a Password Manager to generate them is the easiest solution to this but if one is not used then a combination of upper and lower case letters plus numbers and special characters will all help improve the strength of passwords.
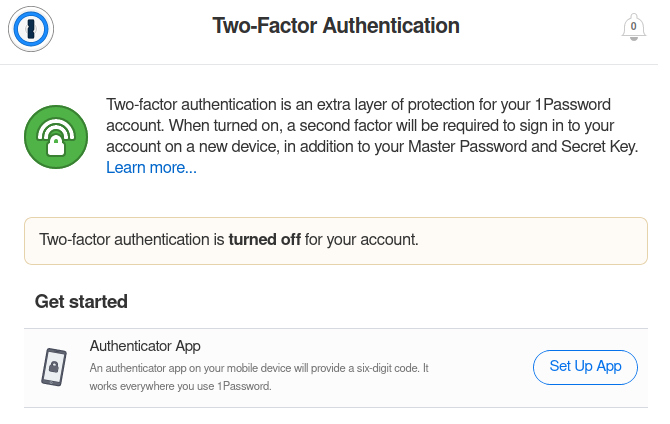
- Two-Factor Authentication (2FA) – this is when an additional level of security is added on top of using a username/password combination. There are a variety of methods employed by web sites and a number of them are facilitated by a smartphone e.g.
- Authenticator (physical device or app) – provides a random number that synchronizes with the web site being accessed.
- Automated voice calls – the web site links to a service whereby a phone call is placed to your cell phone number for confirmation of your identity.
- Password letters – in addition to entering a password you may be prompted to enter say the 2nd, 4th & 8th character.
- PIN – an additional Pin Code may be entered to access the web site.
- Secret question – if you need to reset a password or additional verification is needed then a number of secret questions and associated answers can be setup. If prompted for one of these questions then the correct answer needs entering.
- SMS – a verification number is sent to the cell phone you have registered against your web site account. This then needs entering and verifying to gain access.
- Virtual Private Network (VPN) – to make a connection to the Internet more secure, by ensuring the traffic is encrypted and that your identity is protected, a VPN can be used. See our previous article, Does a VPN keep you Safe & Secure?
Are you involved with web site security? If so what are your opinions on how best to defend against malicious attacks? Please share your thoughts in the comments below.