In our previous article, Network Scanning Tools (part 1), we briefly covered arping and described it as:
ARP stands Address Resolution Protocol and is used for mapping an IP address onto the Ethernet address (MAC address) of a computer that is connected to a network. The arping utility is run via the CLI (Command Line Interface) and sends ARP requests to a specified host and displays the replies. It is similar to performing a ping.
In this article we are going to delve deeper into this tool and work through some examples of using it.
Tool Usage
The synopsis or syntax of arping v2.21 is as follows:
arping [-0aAbBdDeFhpqrRuUv] [-S host/ip] [-T host/ip]
[-s MAC] [-t MAC] [-c count] [-i interface]
[ -w seconds ] [ -W seconds ] [ -V vlan]
[ -Q priority ] [ -g group ] <host | -B>The main options are as follows:
- -S host/ip
- Like -b and -0 but with set source address. Note that this may get the arping unanswered if the target does not have routing to the IP. If you don’t own the IP you are using, you may need to turn on promiscuous mode on the interface (with -p). With this switch you can find out what IP-address a host has without taking an IP-address yourself.
- -T host/ip
- Use -T as target address when pinging MACs that won’t respond to a broadcast ping but perhaps to a directed broadcast.
- -s MAC
- Set source MAC address. You may need to use -p with this.
- -t MAC
- Set target MAC address to use when pinging IP address.
- -c count
- Only send count requests.
- -i interface
- Don’t guess, use the specified interface.
- -w seconds
- Specify a timeout before ping exits regardless of how many packets have been sent or received.
- -W seconds
- Time to wait between pings.
- -V vlan
- VLAN tag to set. Defaults to no VLAN tag.
- -Q priority
- 802.1p priority to set. Should be used with 802.1Q tag (-V). Defaults to 0.
- -g group
- setgid() to this group instead of the nobody group.
Other options referred to above and are available:
- -0
- Use this option to ping with source IP address 0.0.0.0. Use this when you haven’t configured your interface yet. Note that this may get the MAC-ping unanswered. This is an alias for -S 0.0.0.0.
- -b
- Like -0 but source broadcast source address (255.255.255.255). Note that this may get the arping unanswered since it’s not normal behavior for a host.
- -B
- Use instead of host if you want to address 255.255.255.255.
- -p
- Turn on promiscuous mode on interface, use this if you don’t “own” the MAC address you are using.
- -aAdDeFhqrRuUv
- See help page using man arping command for explanation of these options.
Note: Later versions do include additional options not covered above.
Test Environment
For the purposes of this article we are going to be using VirtualBox 6.1 running on top of a Linux desktop computer built with Ubuntu 20.10. Our virtual machines (VM’s) will be the following running on the same NAT Network:
- Kali Linux 2020.4:
- Penetration Testing host to run arping.
- Default login = kali / kali
- IP = 10.0.2.15
- MAC = 08:00:27:ab:08:1c
- Metasploitable 2:
- Extremely vulnerable target.
- Default login = msfadmin / msfadmin
- IP = 10.0.2.4
- MAC = 08:00:27:e9:d3:d7
- Ubuntu 21.04:
- Standard distro Linux target.
- User login = ubuntu / Ubuntu0!
- IP = 10.0.2.5
- MAC = 08:00:27:cd:fe:4b
- Windows 10:
- Standard distro target running MS Edge.
- Default login = IEUser / Passw0rd!
- IP = 10.0.2.6
- MAC = 08:00:27:42:90:70
We also tried to run a macOS target but the VM was too problematic to setup and configure and did not boot with the default image.
Demonstrations
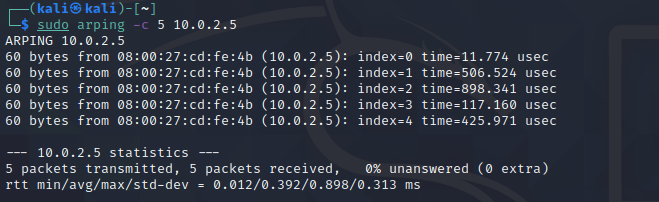
1) ARP known destination 5 times
arping a known IP address using the count (-c) option 5 times returns the following:
2) ARP unknown destination 3 times
arping an unknown IP address (i.e. not assigned to a host) using the count (-c) option 3 times returns the following:
3) ARP with 2 second wait between pings
arping a known IP address with a 2 second gap between each of the 4 pings returns the following:
4) ARP using a specified interface
arping a known IP address using a specified interface, determined using the ifconfig command, for 6 times returns the following:
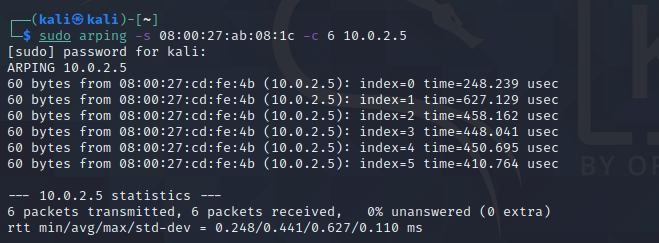
5) ARP using a source MAC Address
arping a known IP address using a source MAC Address, determined using the ifconfig command, for 6 times. This is an alternative method of carrying out example #4 and returns the following:
6) ARP using a source IP Address
arping a known IP address using a source IP Address, determined using the ifconfig command, for 3 times. This is an alternative method of carrying out examples #4 & 5 and returns the following:
Further information
- Homepage & Download:
- Documentation:
arping is distributed and freely available under the GPLv2 (GNU General Public License v2.0).
Do you have any tips or suggestions regarding the use of arping? If so please comment below.