In a previous article, Network Scanning Tools (part 1), we briefly covered ike-scan and described it as:
IKE stands for Internet Key Exchange and is a standard protocol for ensuring security whilst establishing a VPN (Virtual Private Network) connection.
ike-scan is a tool for discovering and fingerprinting IKE hosts i.e. VPN servers. IKE servers can be found by performing an ‘ike’ search at shodan.io.
Below are some of the key functions which ike-scan can perform:
- Discovery – determine which hosts in a given IP address range are running IKE. Hosts that respond to IKE requests are displayed.
- Fingerprinting – determine which IKE implementation hosts are using. This is performed in two ways:
- UDP backoff – records the times of IKE response packets and compares the observed retransmission backoff pattern against known patterns.
- Vendor ID – payloads from VPN servers are compared against known vendor id patterns.
- Transform Enumeration – find which transform attributes are supported by the VPN server for IKE Phase-1 e.g. encryption algorithm, hash algorithm etc.
- User Enumeration – discover valid VPN usernames.
- Pre-Shared Key Cracking – perform offline dictionary or brute-force cracking for IKE Aggressive Mode with Pre-Shared Key authentication. The following are used:
- ike-scan to obtain the hash and other parameters.
- psk-crack to perform the cracking.
In the following sections we are going to look at ike-scan in more detail and demonstrate its use with some examples.
Tool Usage
The synopsis or syntax of ike-scan is as follows:
ike-scan [options] [hosts...]Targets can be specified as follows:
- IP addresses for specified hosts e.g. 192.168.1.10 192.168.1.25
- hostnames for specified hosts e.g. abc.com shop.def.net
- IPnetworks/bits for all hosts in a network e.g. 192.168.1.0/24
- IPstart-IPend for all hosts in a range e.g. 192.168.1.10-192.168.1.25
- IPnetwork:NetMask for all hosts in a network & mask e.g. 192.168.1.0:255.255.255.0
The main options are as follows:
- -f filename
- Read hostnames or IP addresses from the specified filename instead of from the command line.
- -o time
- Display backoff fingerprint table. The time parameter specifies how long to wait in seconds after receiving the last packet, default = 60.
- -2
- Use IKE version 2 which causes outgoing packets to use IKEv2 format.
There are many other options which can be viewed by issuing the following command:
man ike-scanTest Environment
For the purposes of this article we will be using ike-scan v1.9.4 installed on a Raspberry Pi Model 3B+ (192.168.1.32) running Kali Linux 2019.4. Our target VPN servers with IKE support were obtained by searching shodan.io for the term ‘ike’.
Demonstrations
1) IKE detection against a single IP address
IKE detection was run against a single target by specifying the IP address with all options were left as defaults:
2) IKE detection against a single hostname
IKE detection was run against a single target by specifying the hostname with all options were left as defaults:
3) IKE detection against multiple targets
IKE detection was run against multiple targets by specifying the hostname of one and IP address of another. All options were left as defaults:
4) IKE detection against multiple targets from file
IKE detection was run against multiple targets by specifying the hostname of one and IP address of another in a text file. All options were left as defaults and the text file was used as input:
5) IKE detection against a single IP address & display fingerprint table
IKE detection was run against a single target by specifying the IP address and the ‘showbackoff (-o)’ option was used:
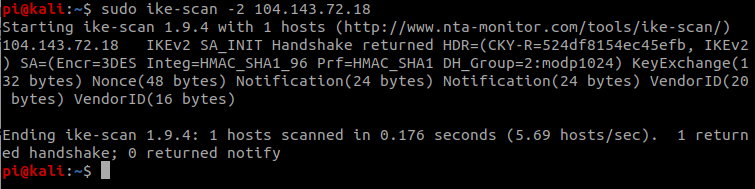
6) IKE version 2 detection against a single IP address
IKE detection was run against a single target by specifying the IP address with all options left as defaults except for specifying IKE version 2. This causes outgoing packets to use IKEv2 format:
Further Information
- Homepage, Download & Documentation:
Ever used the ike-scan tool? If so for what purpose and how useful was it? Please comment below to share your thoughts and experiences.