In a previous article, Network Scanning Tools (part 1), we briefly covered Kismet and described it as:
Kismet is a wireless network and device detector, sniffer, wardriving tool, and WIDS (Wireless Intrusion Detection System) framework.
The tool’s website further describes it as:
Kismet works with Wi-Fi interfaces, Bluetooth interfaces, some SDR (software defined radio) hardware like the RTLSDR, and other specialized capture hardware.
kismetwireless.net
In this, the first of a two part article, we look at Kismet in more detail and walk-through the Home screen, pop-ups and features.
Tool Usage
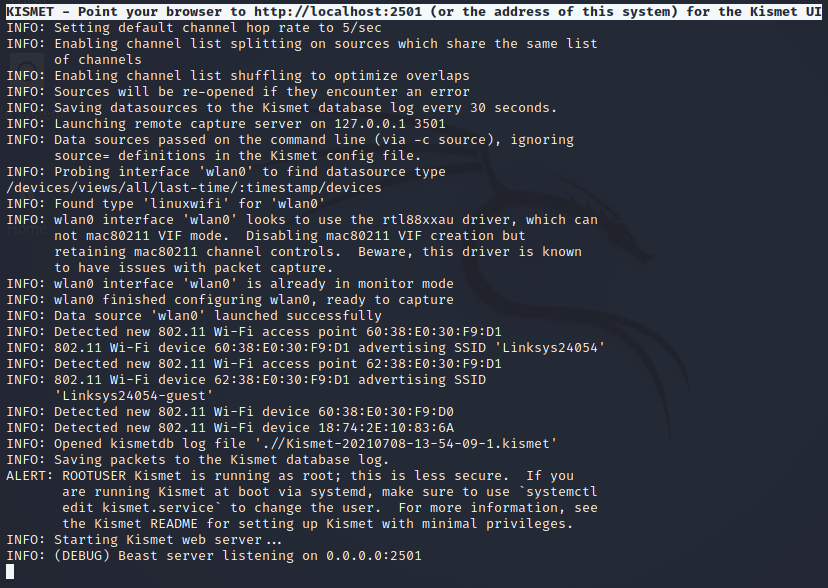
First of all it is necessary to start the Kismet Web Server from the CLI (Command Line Interface) and to specify which wireless adapter to use via the ‘-c’ option. This wireless adapter needs to support Monitor Mode and the start-up command is as follows:
kismet -c wlan0This will then go through the following startup sequence:
Kismet has a variety of other startup options that are described in the ‘man page’ (run the command: man kismet). In addition to command line startup options there are a number of configuration files which can be modified to include a variety of settings – see here for more.
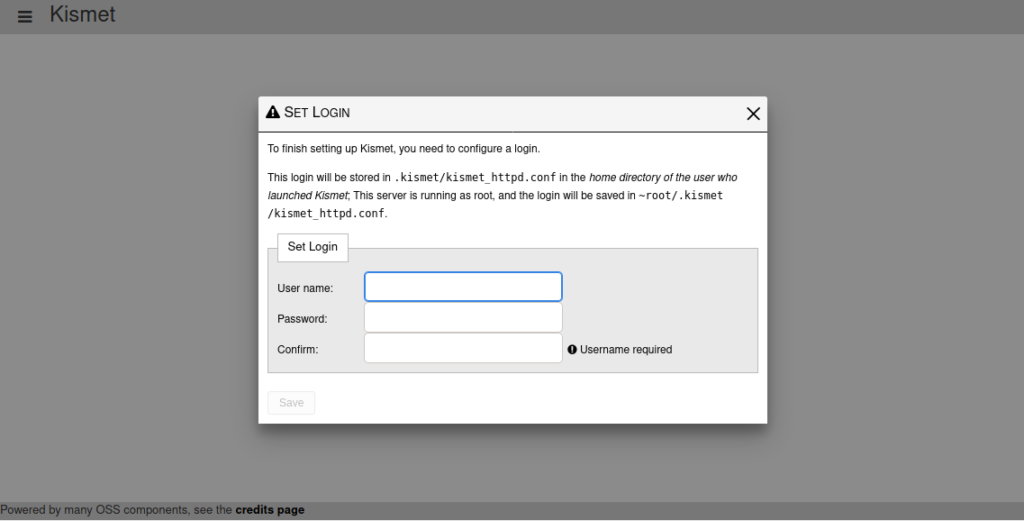
Once started, Kismet is now accessible via a web browser at http://localhost:2501. When accessing the tool for the first time it is necessary to finish the setup by creating a Username & Password:
In the Walk-through section we will examine some of Kismet’s features together with the various information available.
Test Environment
For the purposes of this article we will be using Kismet v2020-09-R4 installed on a Kali Linux 2021.2 virtual machine running within VirtualBox 6.1.
Walk-through
All the following examples are using a wireless adapter (wlan0).
1) Home screen
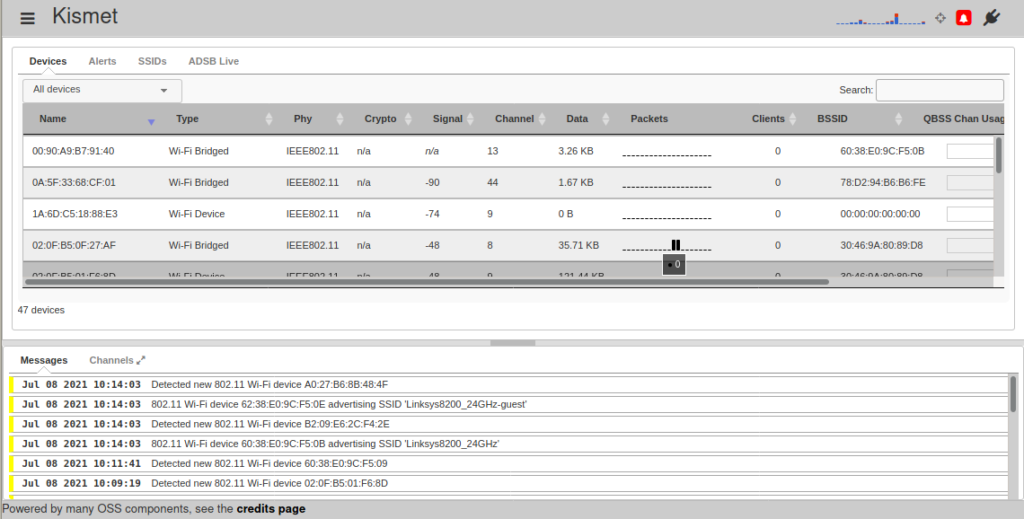
The home screen of the Kismet app looks as follows:
The screen is divided into three main sections with the contents of each being as follows:
a) Header
The top bar of the screen comprises of:
(i) ‘hamburger’ menu
This dropdown menu provides access to additional pop-up screens:
(ii) Scanner graphic
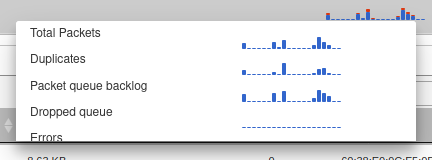
Clicking on the graphic displays scanning details as a pop-up and hovering over each bar shows a breakdown overview:
(iii) Alerts
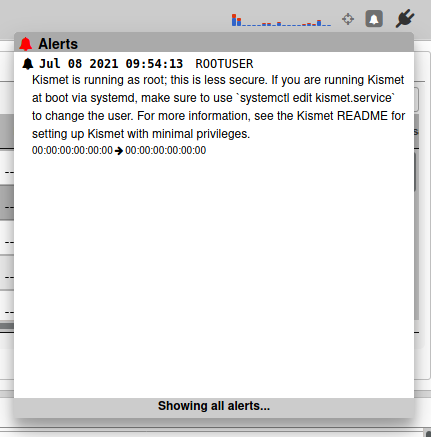
Between the GPS and Power icons on the right of the Header is an Alerts icon. When clicked it shows a pop-up of the latest alert messages:
b) Body
The center section of the screen comprises of the following information in table format with four tabs:
(i) Devices
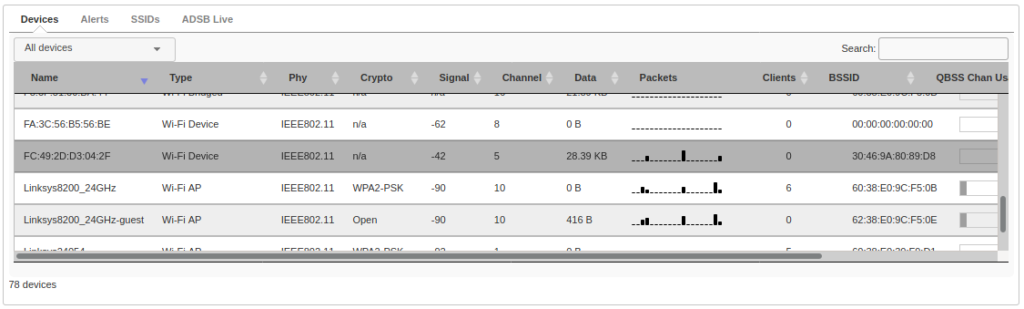
By default ‘All devices’ are displayed and the information is updated in real-time. Each entry is a device that has been detected:
The information displayed about each device is as follows:
- Name – MAC Address of device.
- Type – Type of Wi-Fi e.g. AP (Access Point), Bridged.
- Phy – Physical Type e.g. IEEE802.11, Bluetooth.
- Crypto – encryption used e.g. WPA2-CCMP, WPA2-PSK.
- Signal – strength of signal.
- Channel – number of WiFi channel being used.
- Data – amount of data being transmitted e.g. 180 B, 54.64 Kb.
- Packets – visualization of the packets being detected.
- Clients – number of clients connected to the device.
- BSSID – Basic Service Set Identifier which is the MAC Address of the router or access point.
- QBSS Chan Usage – QoS (Quality of Service) enhanced basic service set i.e. utilization of the channel.
The ‘All devices’ tab is a dropdown menu that allows filtering of the table contents and each column is sortable in ascending or descending order.
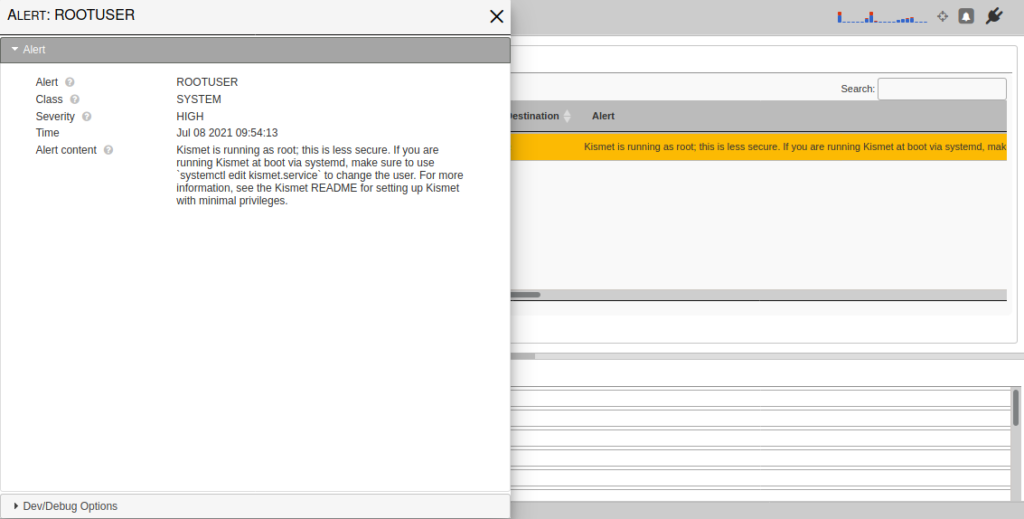
(ii) Alerts
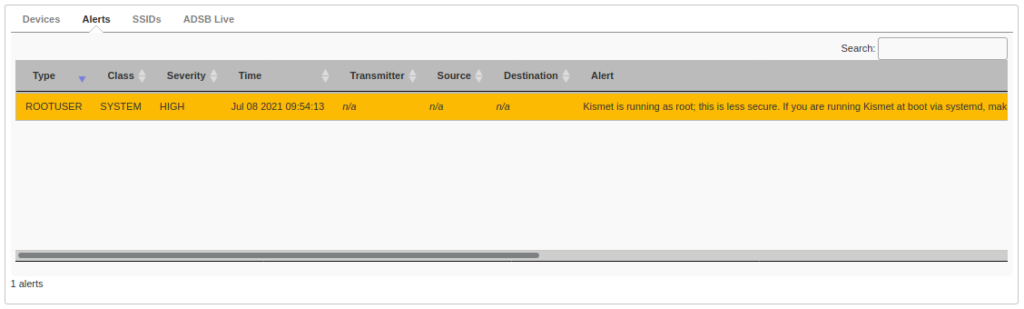
This tab shows a list of alerts with each column being sortable and the list being searchable too:
Clicking on an individual alert displays the information in a more readable format with the line wrapping of text and the option of clicking on the ‘Dev/Debug Options’ at the bottom:
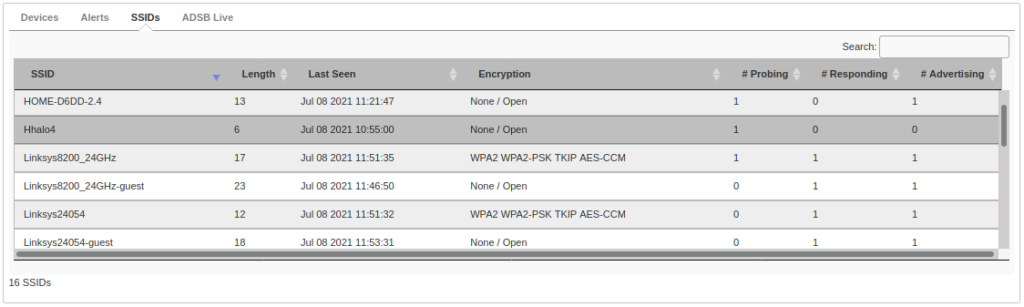
(iii) SSIDs (Service Set IDentifier)
This tab shows a list of detected routers or access points with each column being sortable and the list being searchable too:
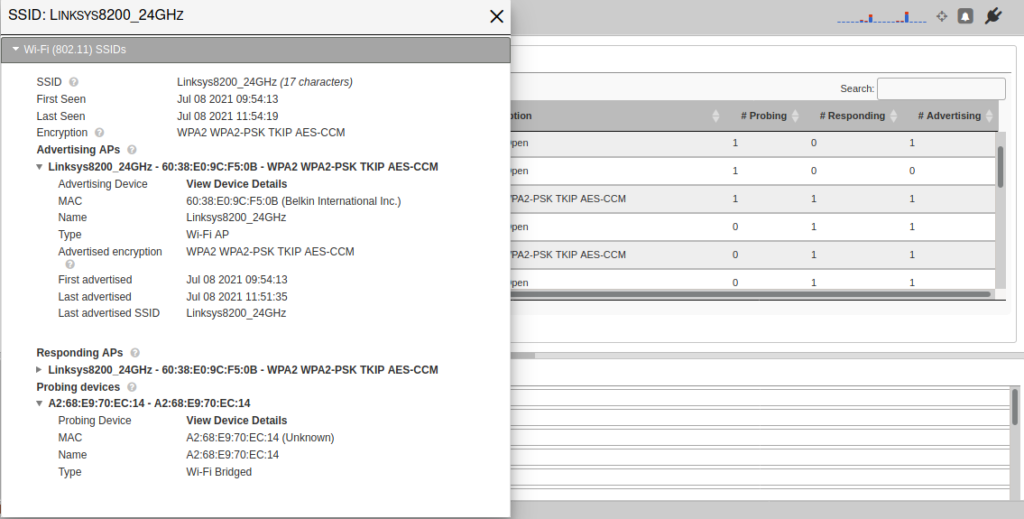
Clicking on an individual SSID displays the information in a more readable format with the option of expanding the ‘Advertising APs’, ‘Responding APs’ and ‘Probing devices’ sections:
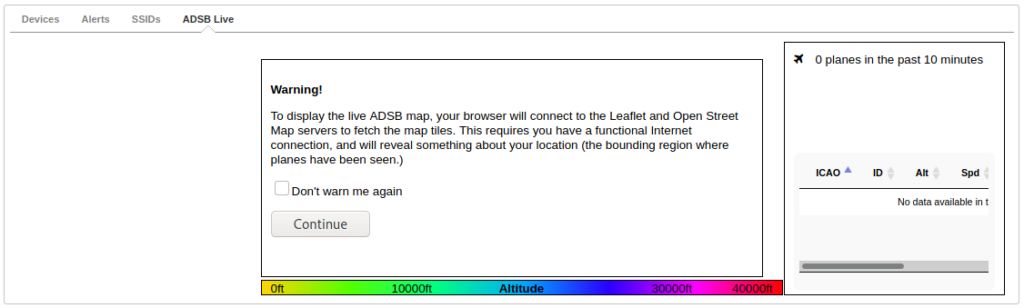
(iv) ADSB Live (Automatic Dependent Surveillance–Broadcast)
This tab shows a map of planes within your area:
c) Footer
The bottom section of the screen comprises of the following:
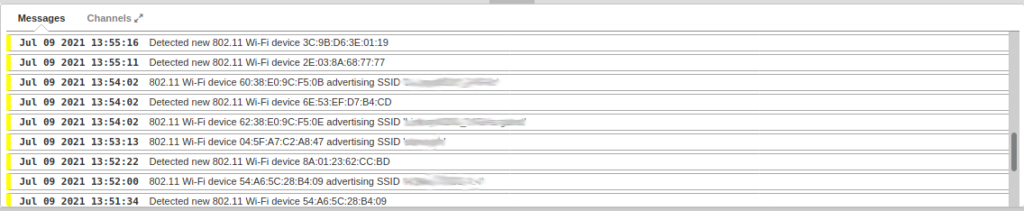
(i) Messages
This section is effectively a log of what the Kismet server is detecting. It shows the date and time of each detection together with information about the router, access point or other type of wireless device. This information includes the physical type, MAC Address, and SSID of the device itself as shown below. The SSID names are blurred for privacy:
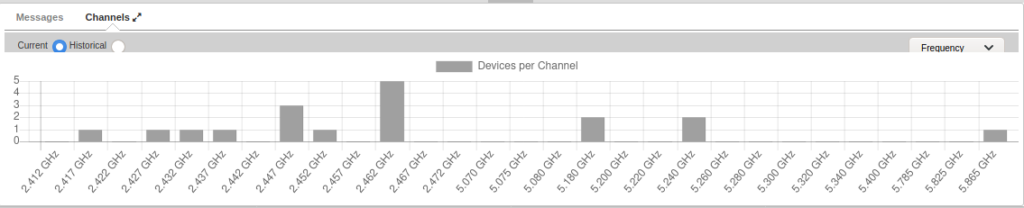
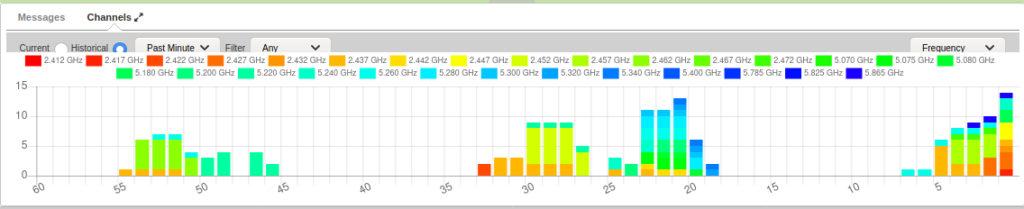
(ii) Channels
This section is split into two sets of WiFi channel detection information, namely Current and Historical.
The Current Channels shows a graph with the frequency of each channel in GHz and the number of devices per channel. This can be expanded to a larger pop-up window and filtered by Frequency:
The Historical Channels shows a different graph of the number of devices over the Past Minutes, Past Hour, and Past Day with each frequency represented as a different color. It is possible to apply a Filter and only show an individual frequency too:
Further Information
- Homepage:
- Download:
- Documentation:
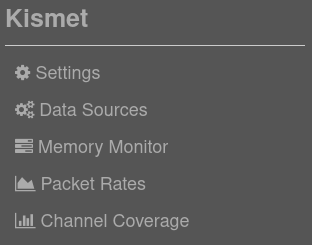
In part two of this article we will continue the walk-through of the Kismet and look at Settings, Data Sources, Memory Monitor, Packet Rates, and Channel Coverage.
Do you have experience with using Kismet for wireless detection? If so please comment below with any tips.