In a previous article, Network Scanning Tools (part 1), we covered legion at a high-level and the developers describe it as follows:
Legion, a fork of SECFORCE’s Sparta, is an open source, easy-to-use, super-extensible and semi-automated network penetration testing framework that aids in discovery, reconnaissance and exploitation of information systems.
GoVanguard
Below are some of the core features of legion:
- Automatic recon & scanning – this is performed using around 100 scripts that are automatically scheduled. These include DirBuster, Hydra, nikto, NMAP, SMBenum, SSLyze, Vulners, whataweb, WebSlayer and more.
- Automatic detection of CPEs & CVEs:
- CPE = Common Platform Enumeration – a standardized method of describing and identifying classes of applications, operating systems, and hardware devices present among an enterprise’s computing assets.
- CVE = Common Vulnerabilities & Exposures – a system that provides a reference-method for publicly known information-security vulnerabilities and exposures.
- Ties CVEs to Exploits – these are obtained from the Exploit Database.
Other features include:
- Easy to use GUI (Graphical User Interface) – to quickly find and exploit attack vectors on hosts.
- Modular functionality – for easy customization and the automatic calling of scripts and tools.
- Highly customizable – stage scanning for IPS (Intrusion Prevention System) evasion.
- Realtime autosaving – of project results and tasks.
In the upcoming sections we are going to look at legion in some detail and demonstrate it with some examples.
Tool Usage
The synopsis or syntax of legion is as follows:
./startLegion.shor on the likes of Kali there is a menu option available.
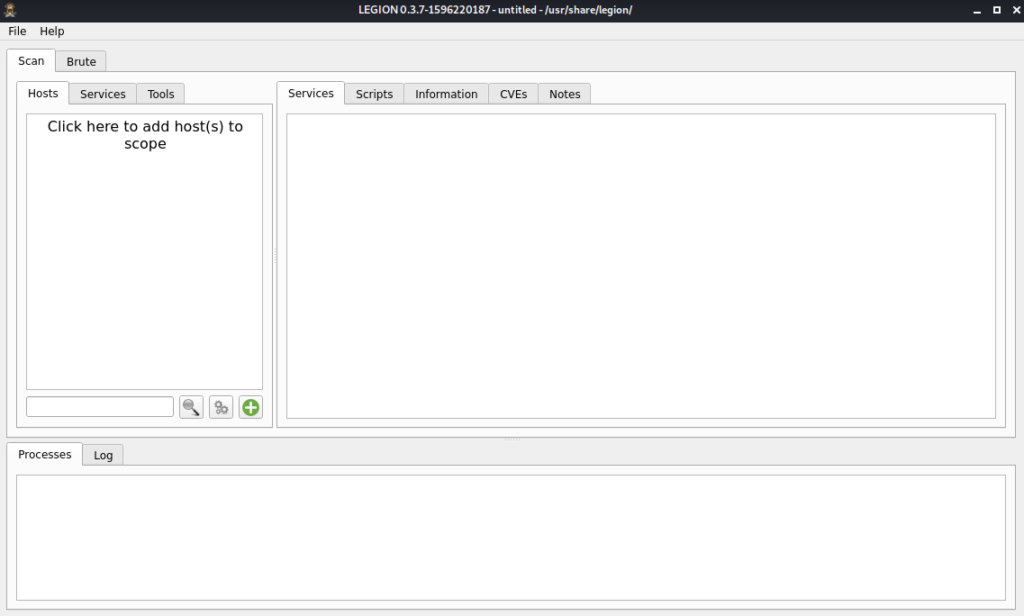
The startup screen is as follows:
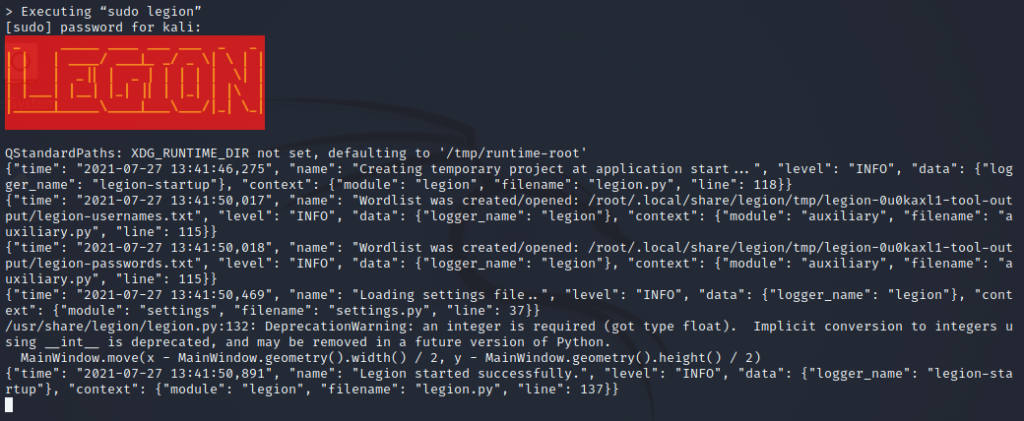
Behind the scenes the following is being run from within the startup shell script for legion, this acts as a server to the front-end:
Test Environment
For the purposes of this article we will be using legion v0.3.7 installed on a Kali Linux 2021.2 virtual machine (IP = 10.0.2.15) running within VirtualBox 6.1. The target machines are being run as virtual machines on the same NAT Network:
- Metasploitable 2:
- IP = 10.0.2.4
- MAC = 08:00:27:e9:d3:d7
- Ubuntu 21.04:
- IP = 10.0.2.5
- MAC = 08:00:27:cd:fe:4b
- Windows 10:
- IP = 10.0.2.6
- MAC = 08:00:27:42:90:70
Demonstrations
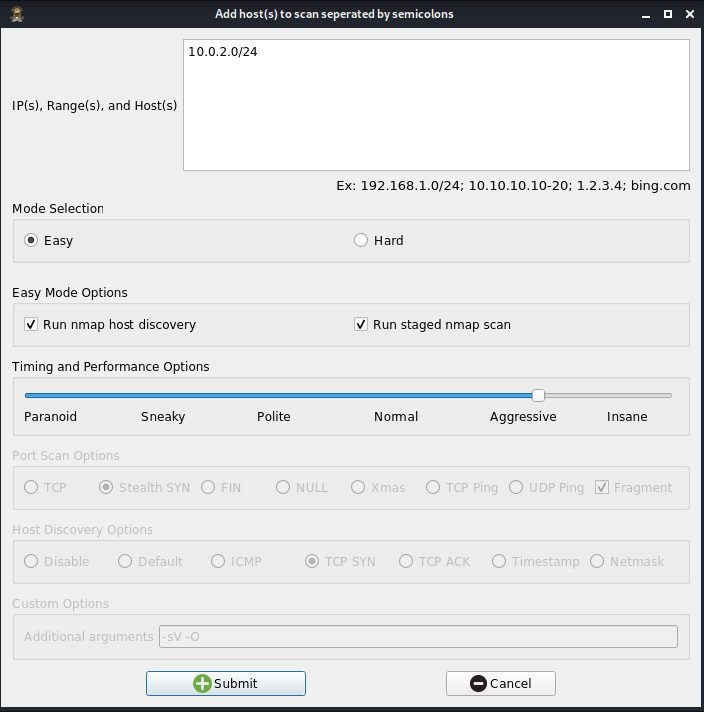
1) Add host(s) to scan
Clicking on the link in the Scan -> Hosts section of the startup screen allows the inputting of target hosts. These can be specified as follows:
- IP Addresses e.g. 10.0.2.5 or 10.0.2.5; 10.0.2.6
- Ranges e.g. 10.0.2.0/24 or 10.0.2.5-6
- Hosts e.g. google.com or google.com; yahoo.com
2) Run NMAP host discovery
Within example #1, whilst adding target hosts, there were two Easy Mode Options:
- Run nmap host discovery
- Run staged nmap scan
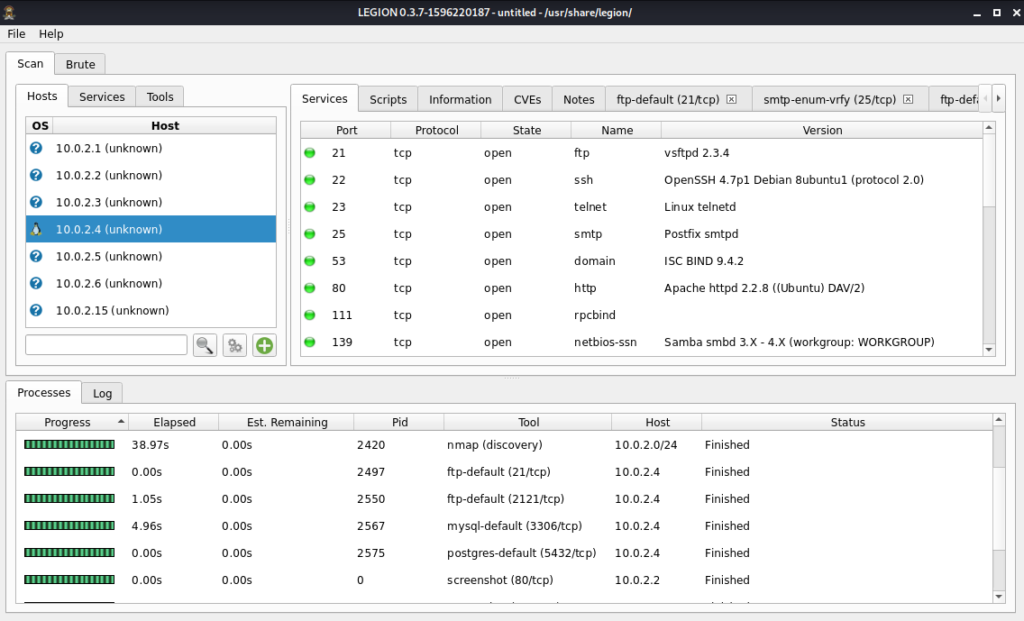
For this example only the first option was selected and the Timing & Performance was set to Normal. The summary results as shown within the legion main screen were as follows:
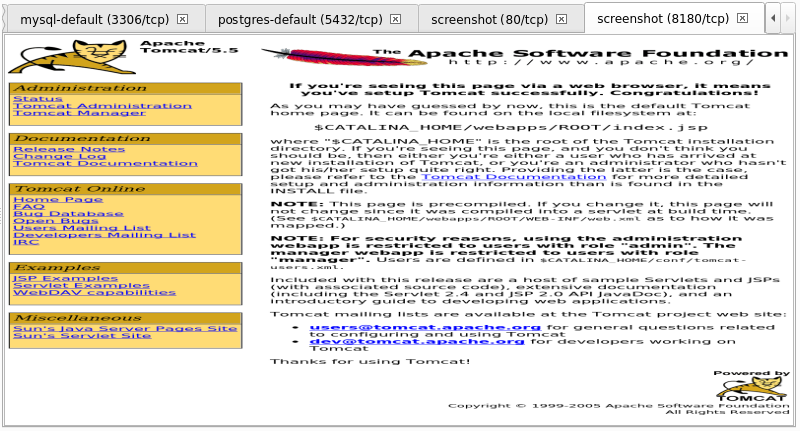
The top Scan section of the screen shows the Hosts discovered on the left side and for the selected one there are a number of tabs on the right side containing a variety of information such as Services, Scripts and more.
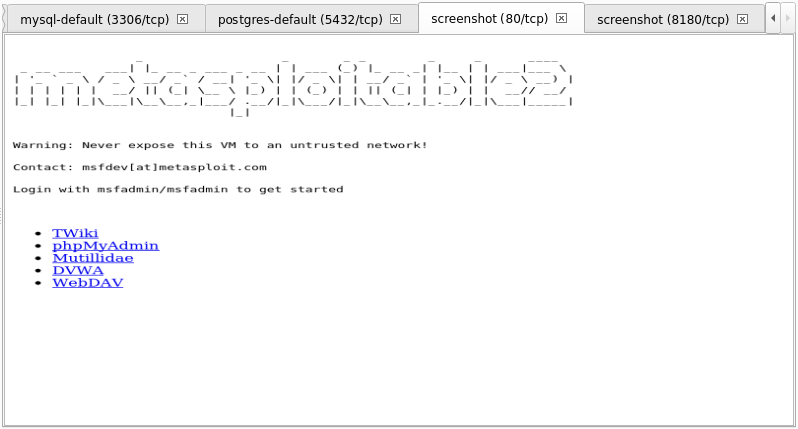
Screenshots can even be captured showing the host’s responses on certain ports e.g. ports 80 and 8180 below:
In the bottom Processes section of the screen there is a list of individual jobs or scripts that that were run by legion together with timing, tool information, target and status details.
3) Run staged NMAP scan
Continuing on from example #2, here we are running the second option with the Timing & Performance set to Normal. The summary results of the 6 x nmap stages run within the legion were as follows and included additional information such as the discovered CVEs:
The bottom section of the above screenshot shows an excerpt of the logging information recorded. Within the Scan section there are two additional tabs which provide alternative views on the same results information i.e. broken down by Services or by Tools.
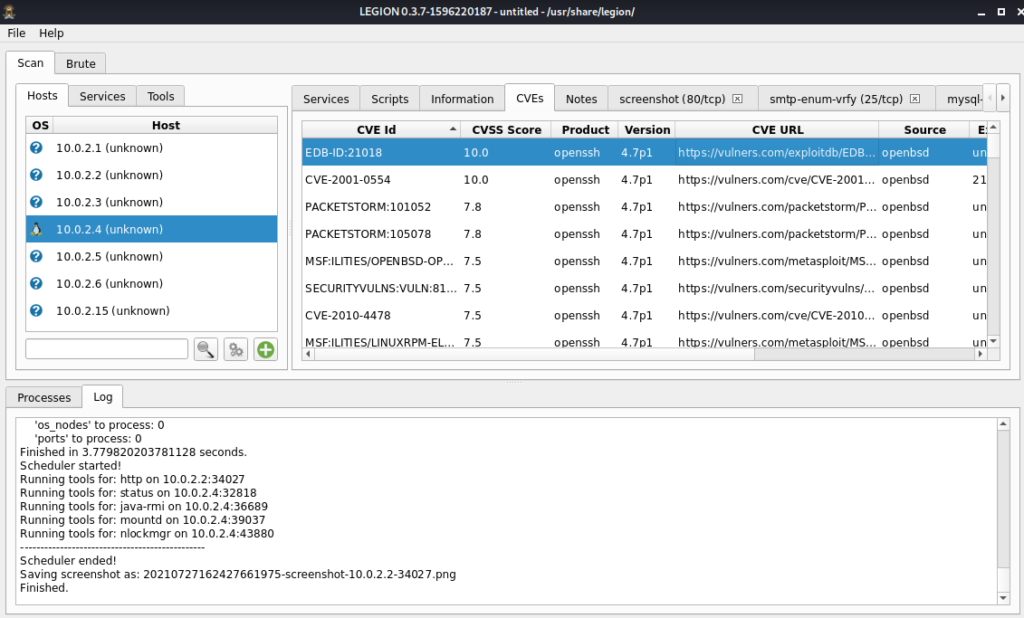
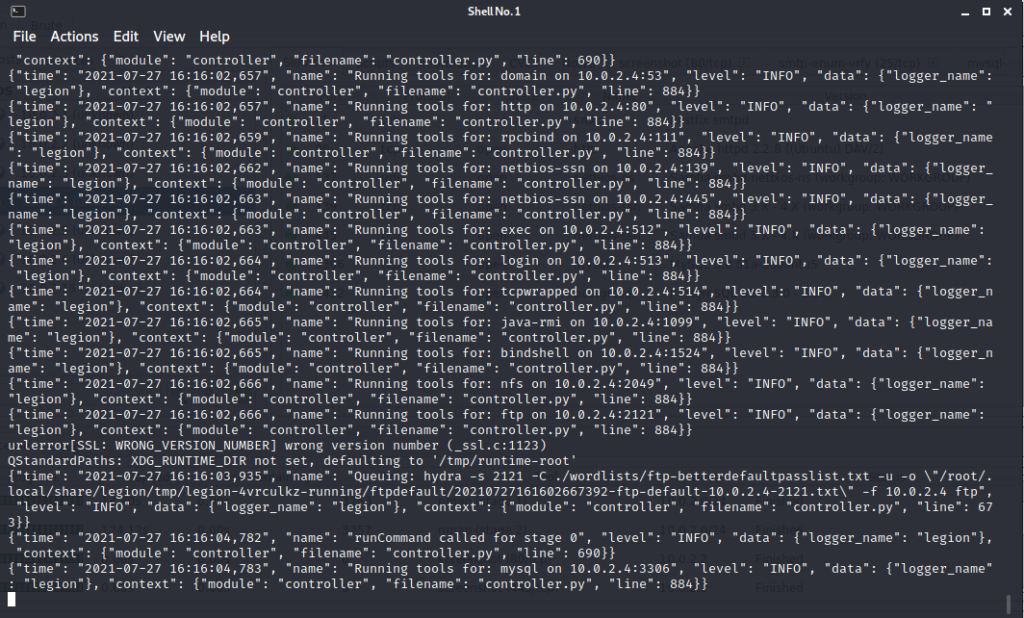
In the background there is a shell script running within a terminal session. This is generating NMAP commands that are then imported one process at a time by the frontend. The background shell looks like this:
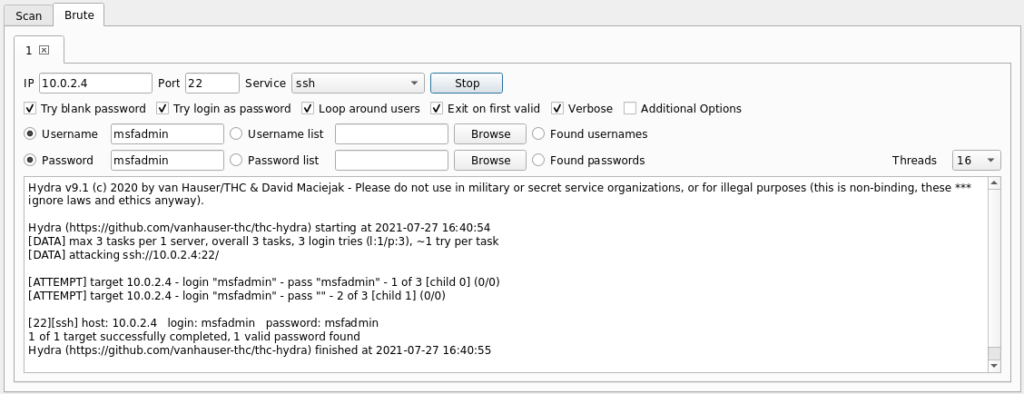
4) Running a Brute Force attack
In addition to the Scan section at the top there is also a one called Brute. This is for running Brute Force attacks against specified targets. There are a variety of parameters which can be specified including the target IP address, port#, service and more. A specific username/password combination can be supplied or lists of usernames and passwords.
In the following example the default login credentials were run against the SSH service on a Metasploitable target:
Further Information
- Homepage, Download & Documentation:
Do you have any experience of using legion for penetration testing networks and devices? If so please share your thoughts in the comments below.